Why Reporting Failures are IT Failures and How to Bridge the Gap Before It's Too Late
Picture this: It's 8:47 PM on a Tuesday. Your CFO just forwarded you an urgent email from the SEC's Division of Enforcement. They're requesting detailed documentation about revenue recognition practices from Q2 2023. Your heart sinks. You know exactly what happened.
There's a Jira ticket somewhere FINREP-2847 or something like that marked "Won't Fix" because it was deprioritized against the shiny new mobile app feature. That ticket represented a critical gap in your financial reporting system. The SEC doesn't care that it was in your backlog. They don't care that you had insufficient sprint capacity. They care about accurate, timely, and compliant financial reporting.
Welcome to the invisible crisis where IT roadmaps collide with regulatory reality.
The Great Disconnect: Finance Speaks, IT Listens (But Doesn't Always Hear)
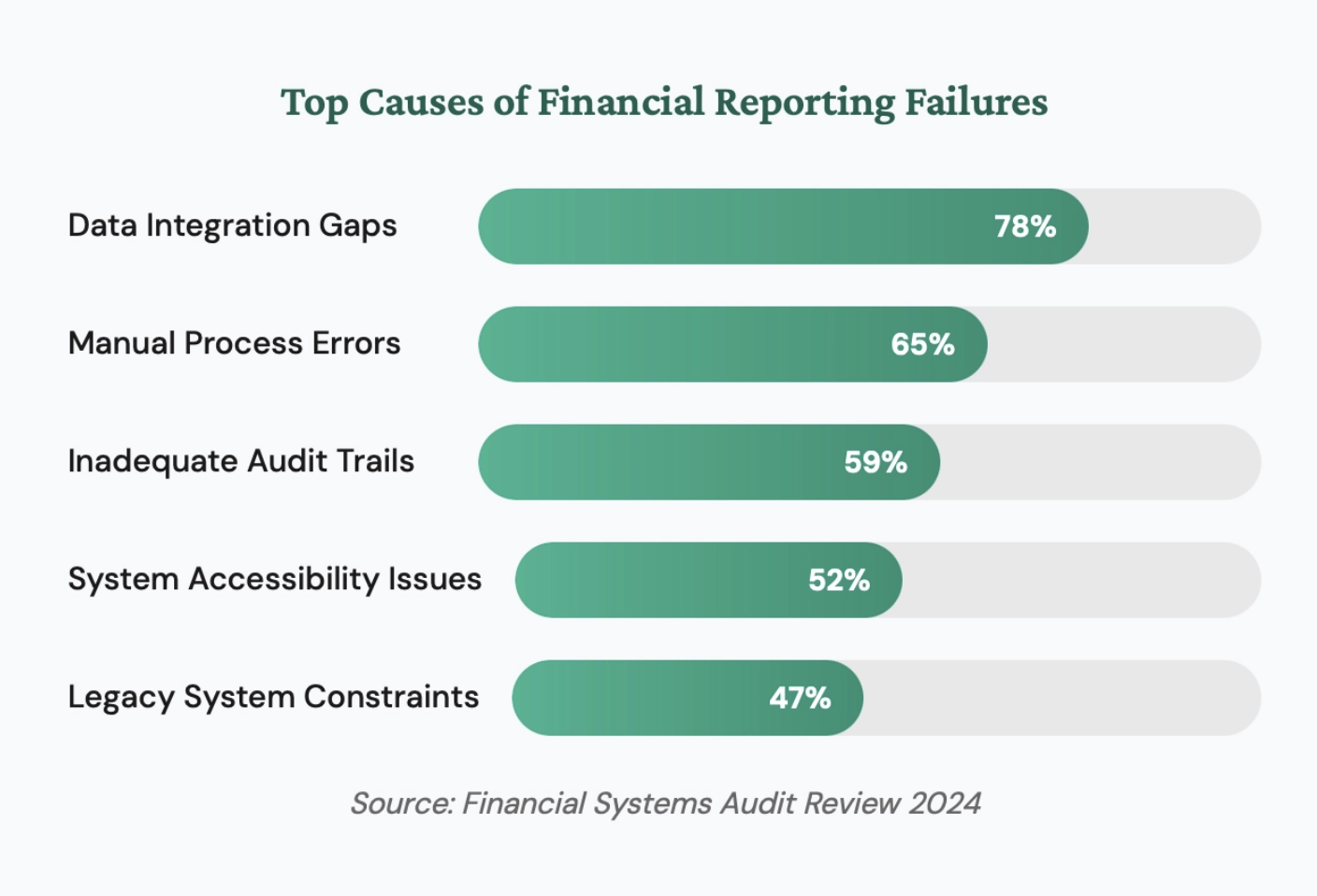
A persistent cultural and operational divide between finance and IT departments is a leading cause of compliance failures. Finance teams define what must be reported while IT teams control how systems work, but critical compliance requirements are routinely lost, deprioritized, or misunderstood when translating regulatory needs into engineering roadmap items.
Financial reporting isn't just about numbers on a spreadsheet. It's about systems, controls, data integrity, and audit trails, all of which live in the IT domain. Yet, there's a persistent cultural and operational divide between finance teams and IT departments that consistently leads to compliance failures. According to a Gartner survey, 65% of CFOs cited misalignment between finance and IT as a top risk factor for reporting errors (Gartner, 2024). SEC Chief Accountant Paul Munter stated in a 2023 speech that "financial reporting is only as reliable as the systems and controls that produce it."
Finance teams understand what needs to be reported. IT teams understand how systems work. But somewhere in the translation between "We need automated revenue recognition" and "Let's add it to the Q3 roadmap," critical compliance requirements get lost, deprioritized, or misunderstood.
The Anatomy of a Preventable Disaster
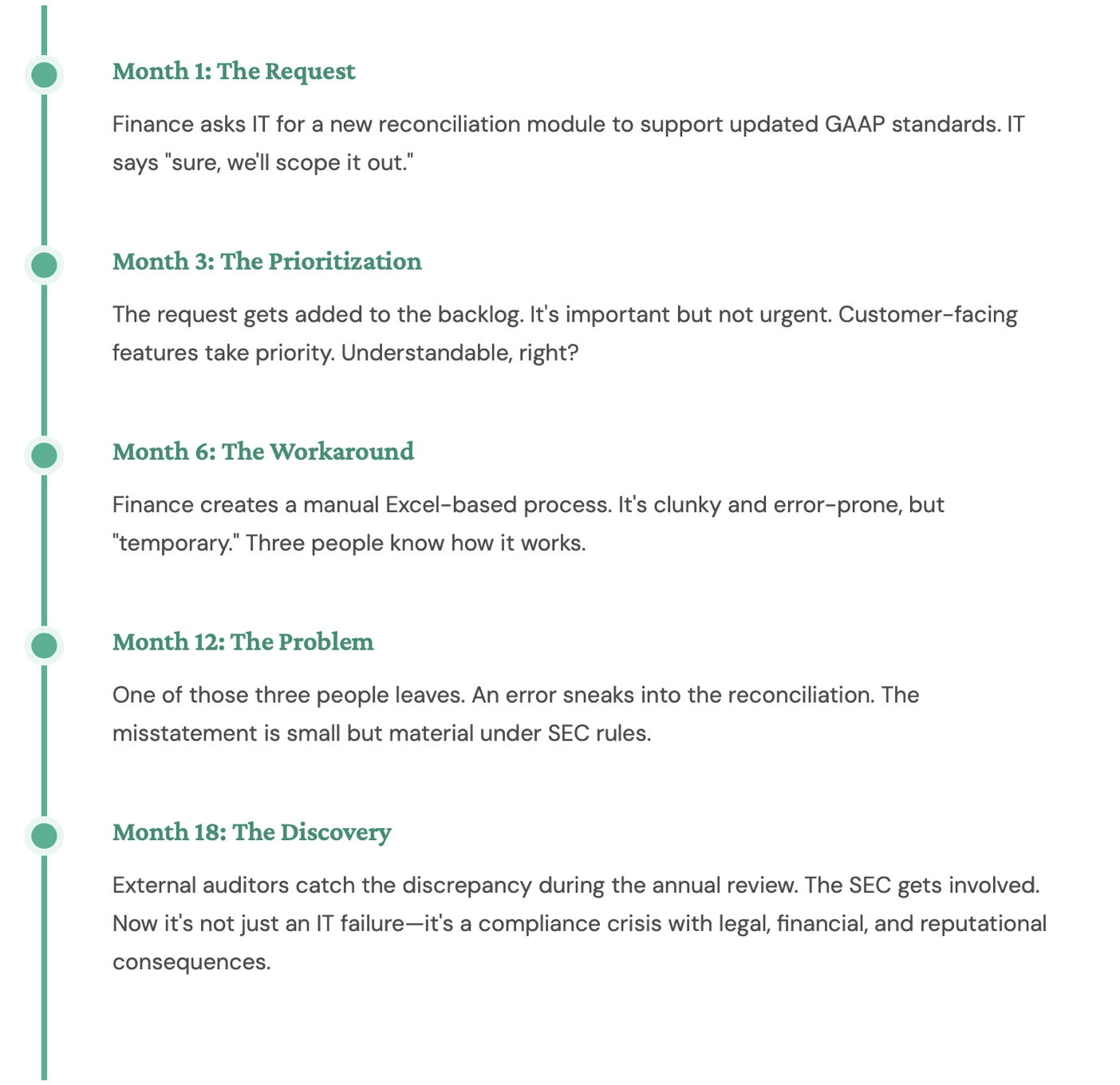
A typical preventable reporting disaster follows a predictable pattern: a finance team identifies a system gap, IT deprioritizes the fix against product features, a manual workaround is created, that workaround introduces data integrity risks, and eventually an audit or SEC inquiry exposes the deficiency. The average financial restatement costs $11.7 million in penalties, legal fees, and stock price impact.
Let's break down how a typical reporting failure unfolds and how it's almost always an IT failure in disguise.
The Hidden Cost
The average cost of a financial restatement is $11.7 million when you factor in penalties, legal fees, audit costs, and stock price impact. A study by Audit Analytics found that restatement filings increased 12% between 2022 and 2024 (Audit Analytics, 2024). That cost is significantly more than the expense of building the system correctly from the start.
Why IT Failures ARE Reporting Failures
In modern enterprises, every financial reporting failure is inherently an IT failure because internal controls are embedded in systems, financial statements are data products dependent on IT infrastructure, audit trails require digital logging and lineage tracking, and manual processes no longer provide adequate controls or scalability for regulatory compliance.
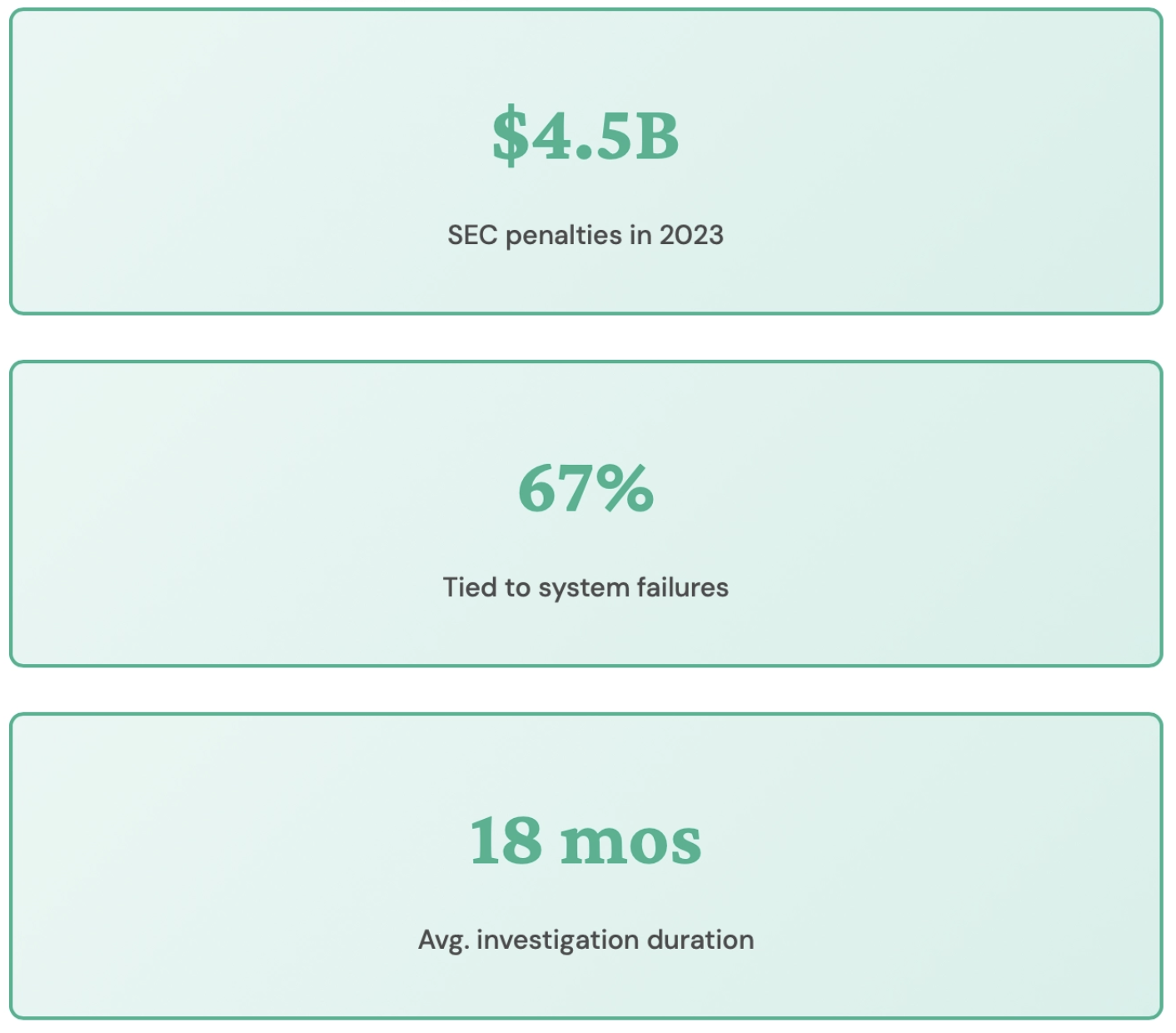
Here's the uncomfortable truth that boards and executives need to understand: In modern enterprises, there is no such thing as a "pure" financial reporting failure that isn't also an IT failure. The PCAOB's 2024 inspection findings consistently identify IT-related internal control deficiencies as a leading cause of audit failures (PCAOB, 2024).
1. Systems Are Your Controls
Internal controls over financial reporting (ICFR) aren't just policies and procedures documented in binders. They're embedded in your systems. When your ERP doesn't enforce proper authorization hierarchies, when your data warehouse allows unaudited manual adjustments, when your reporting tool lacks proper version control these aren't IT bugs. They're control deficiencies that will show up in your SOX 404 report.
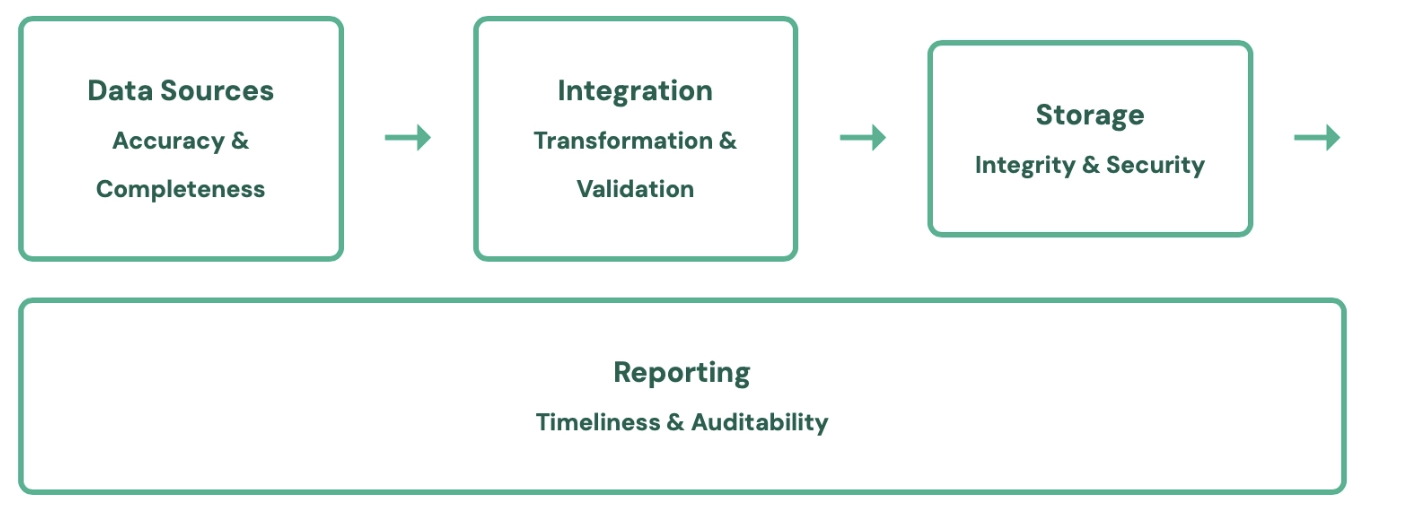
2. Data Is the Product
Your financial statements are a data product. Like any data product, their quality depends on:
If any link in this chain breaks, your financial reporting is compromised. These are all IT responsibilities.
3. Audit Trails Are Digital Evidence
The SEC doesn't just want to see the final numbers. They want to see the entire lineage: who entered what data, when, from which system, with what authorization, and how it flowed through to the final report. This requires robust logging, versioning, and data lineage tracking all IT capabilities.
4. Automation Isn't Optional Anymore
Manual processes don't scale, don't provide adequate controls, and create unacceptable risk. According to EY's Global Financial Accounting Advisory Services survey, 78% of finance leaders reported that manual close processes led to at least one material error in the prior fiscal year (EY, 2024). The era of Excel-based close processes is over. Modern financial reporting demands system-driven automation with built in controls, and building and maintaining those systems is an IT function.
Real Example: In 2023, the SEC charged GTT Communications with financial reporting violations after the telecommunications company struggled to integrate systems following eight rapid acquisitions. Their two key operational systems couldn't be reconciled, leading to a "persistent and growing discrepancy" in expense data. Despite knowing their systems were inadequate, GTT made over $35 million in unsupported accounting adjustments that inflated operating income by at least 15%. The result? Delisting from NYSE, bankruptcy, and emergence as a private company. The CFO didn't write bad code but the failure to prioritize system integration was ultimately a board level IT governance failure.
Bridging the Gap: What Needs to Change
Bridging the IT-finance divide requires five structural changes: elevating financial systems to Tier 1 critical infrastructure on IT roadmaps, establishing cross-functional governance with joint steering committees, designing compliance-driven system architecture with immutable audit logs, hiring talent that spans both finance and technology, and shifting organizational culture to treat financial system bugs as compliance risks.
Fixing this requires fundamental changes in how organizations think about the relationship between IT and financial reporting. Former SEC Chair Mary Jo White emphasized that "companies must ensure their internal controls, including IT systems, are designed and operating effectively to produce reliable financial reporting." The COSO Internal Control Framework provides a structured approach for integrating IT governance with financial reporting controls.
1. Elevate Financial Systems on the IT Roadmap
Financial reporting systems need to be treated as Tier 1 critical infrastructure, not backlog items that compete with product features. This means:
- Dedicated sprint capacity for financial systems work
- Service level agreements (SLAs) for finance requested changes
- Executive sponsorship that treats these projects as compliance initiatives, not "nice to haves"
2. Create Cross-Functional Governance
Finance and IT can't operate in silos. Organizations need:
- Joint steering committees where finance and IT leadership review compliance related system requirements
- Embedded IT resources within finance teams who understand both accounting principles and system capabilities
- Compliance aware product managers who can translate regulatory requirements into technical specifications
3. Implement Compliance Driven Architecture
Your system architecture needs to be designed with compliance in mind from the ground up:
- Immutable audit logs for all financial transactions
- Automated reconciliation and validation at every integration point
- Role based access controls with full traceability
- Built-in segregation of duties enforcement
- Automated control testing and monitoring
4. Invest in the Right Talent
You need people who can bridge the finance IT divide. This might mean:
- Hiring IT professionals with accounting backgrounds
- Training finance professionals in data engineering and system design
- Creating dedicated "financial systems engineer" roles
5. Change the Culture
Perhaps most importantly, organizations need to fundamentally change how they think about IT's role in financial reporting. IT teams need to understand that:
- A bug in the revenue recognition module is as serious as a security vulnerability
- Technical debt in financial systems carries regulatory risk, not just engineering risk
- When finance says "We need this for compliance," it's not a negotiation it's a requirement
The Bottom Line
That Jira ticket marked "Won't Fix"? It might represent a latent compliance violation. That manual workaround Finance created because IT was too busy? It might be the crack that brings down your entire financial reporting structure during your next audit.
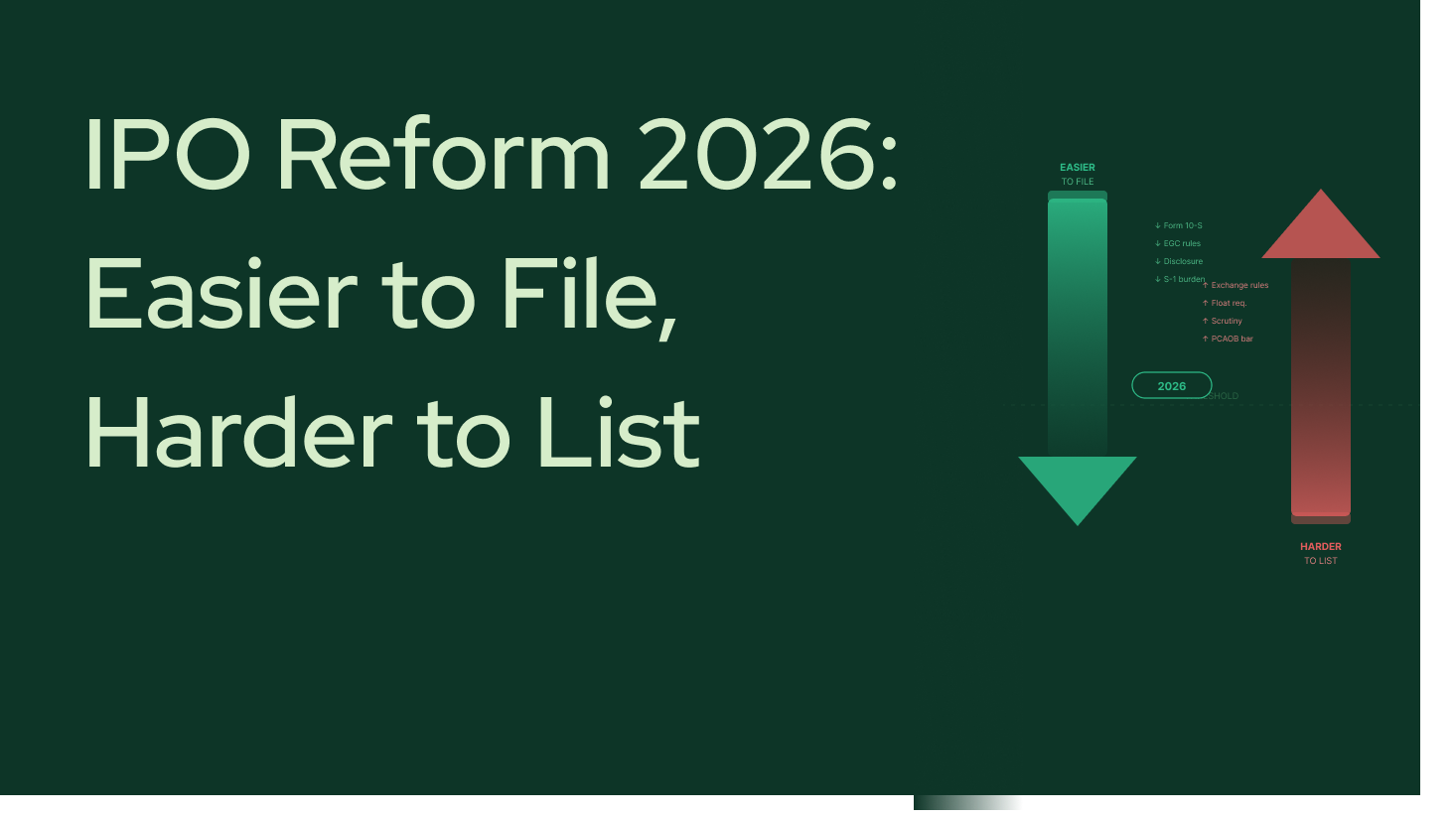
The SEC doesn't care about your IT roadmap. They care about accurate, timely, and compliant financial reporting. And in 2026, that means having the systems, controls, and architecture to support it.
Reporting failures are IT failures. It's time we treated them that way.
The gap between IT execution and regulatory expectations isn't just a technical problem---it's a governance problem, a cultural problem, and increasingly, a board-level risk management problem. According to the SEC's 2024 Annual Report on Enforcement, the Commission brought over 780 enforcement actions in fiscal year 2024, many involving internal controls failures rooted in system deficiencies (SEC, 2024). Organizations that address this gap reduce their exposure to enforcement actions, restatements, and audit deficiencies. Those that do not face escalating regulatory and financial risk.